
This room was released on day nine of the event and focuses on cracking passwords.
Task 1 Introduction
This section introduces some more story material.
Launch the Virtual Machine.
Flag
There is no question or answer for this section.
Task 2 Attacks Against Encrypted Files
Read about password cracking methods.
Change directory to the desktop and check the files there.
file <filename>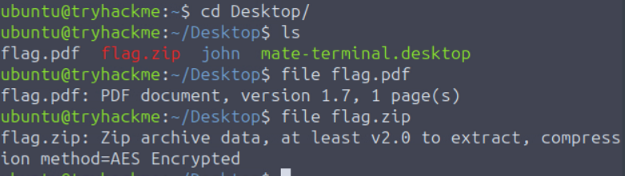
Use PDFCrack on the PDF file to crack the password using the rockyou wordlist. PDFCrack is an open source application created to help crack passwords on PDF documents. The rockyou wordlist emerged from the breach of the RockYou company in 2009 and is commonly used as a password dictionary. It can be found publicly here. A variety of wordlists can be found in the /usr/share/wordlists/ directory on this machine.
pdfcrack -f flag.pdf -w /usr/share/wordlists/rockyou.txt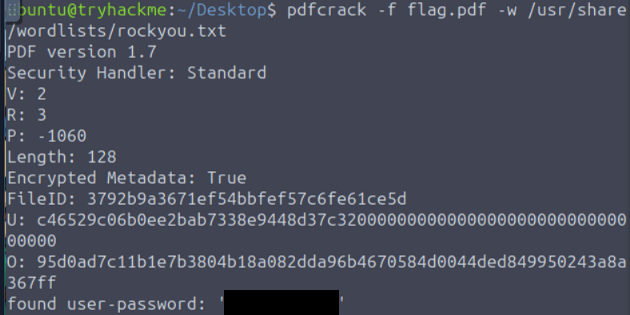
Use the password to open the file and see the flag.
Flag
THM{Cr4ck1ng_PDFs_1s_34$y}
Extract the password hashes from the ZIP file. Zip2john is a terminal tool to extract hashes from ZIP files.
zip2john flag.zip > ziphash.txtCrack the hash using john. John the Ripper is an open source tool for cracking passwords (auditing and recovering passwords) that supports a variety of methods.
john --wordlist=/usr/share/wordlists/rockyou.txt ziphash.txt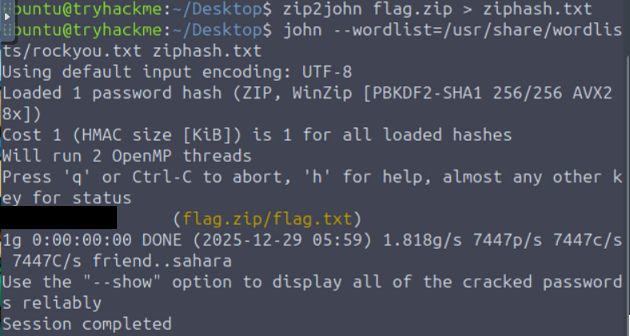
Use the password to open the ZIP file and see the flag.
Flag
THM{Cr4ck1n6_z1p$_1s_34$yyyy}
There is an optional key to get access to a side quest in this machine.