This room was released on day eleven of the event and focuses on Cross Site Scripting (XSS).
Task 1 Introduction
Read a brief setup with a tiny bit of story.
Spin up the Attack Box and a Virtual Machine.
Flag
There is no question or answer for this section.
Task 2 Leave the Cookies, Take the Payload
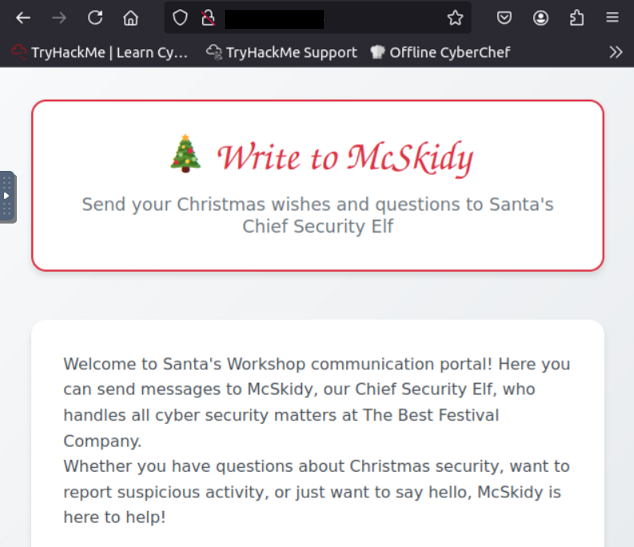
Access the web app dashboard from the Attack Box using the web browser.
Read about Cross Site Scripting (XSS), a vulnerability that arises from improper validation of user input that can result in it being interpreted as code and run.
- Reflected XSS is loaded immediately and results displayed to the user.
- Stored XSS is stored on the web server and delivered to all users.
Flag
Stored
Enter a reflected XSS payload into search box and submit.
<script>alert('Reflected Meow Meow')</script>
Look below the search results on the page for the flag.
Flag
THM{Evil_Bunny}
Enter a stored XSS payload into the comment box and submit.
<script>alert('Stored Meow Meow')</script>Look below recent messages on the page for the flag.
Flag
THM{Evil_Stored_Egg}
